Insight Engine Start 855 432 0401 Revealing Verified Caller Signals

Insight Engine Start 855 432 0401 frames verified caller signals as a layered verification problem. It combines origin data, device fingerprints, and real-time behavioral analytics to differentiate legitimate calls from spoofed ones. The approach emphasizes network attestations and spoofing defenses, while preserving user autonomy and seamless call flow. The methodology aims for standardized risk metrics and auditable processes, supporting evidence-based routing. The implications for trust and efficiency are clear, but practical implementation raises questions that warrant careful consideration.
What Are Verified Caller Signals and Why They Matter
Verified caller signals are indicators derived from a combination of caller authentication data and behavioral patterns used to assess the credibility of incoming calls. The approach quantifies risk through verified signals and standardized metrics, enabling objective evaluation. This framework supports caller verification by distinguishing legitimate attempts from anomalies, reducing uncertainty and empowering informed decisions while preserving freedom to communicate securely and efficiently.
How Insight Engine Start 855 432 0401 Sees Through Spoofing
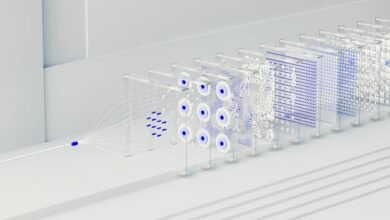
How Insight Engine Start 855 432 0401 combats spoofing through a layered verification framework involves a systematic integration of caller-origin signals, device fingerprints, and real-time behavioral analytics to distinguish legitimate calls from deception.
The approach analyzes insight signals and cross-verifies with network attestations, enabling spoofing defenses that minimize impersonation risk while preserving user autonomy and flow.
Practical Benefits for Businesses and Call Centers
Businesses and call centers can anticipate measurable gains from deploying Insight Engine Start 855 432 0401, with the system delivering improved call integrity, reduced spoofing-related bounce rates, and smoother customer interactions. The approach leverages verified signals to quantify risk and optimize routing, enabling evidence-based decisions. By augmenting caller intelligence, operations gain clarity, efficiency, and resilience in high-volume contact environments.
Implementing Verified Signals: Steps, Pitfalls, and Best Practices
Implementing verified signals requires a structured, evidence-based approach that translates data inputs into actionable routing and risk assessments. The process emphasizes data provenance, validation checks, and continuous monitoring to ensure reliability. Steps include metric definition, source vetting, and incremental rollout. Pitfalls involve overfitting models, data latency, and spoofing risks. Best practices favor transparency, auditability, and iterative refinement for resilient threat detection.
Conclusion
In verifying caller signals, precision guides evaluation, precision guides routing, precision guides trust. In layered verification, signals accrue strength, signals reveal legitimacy, signals deter deception. With device fingerprints, behavioral analytics, and network attestations, risk metrics normalize, decision-making clarifies, outcomes improve. Across enterprises, adoption standardizes, audits validate, transparency reassures. In continuous monitoring, reliability solidifies, resilience builds, continuity persists. Ultimately, verified signals illuminate truth, inform actions, optimize interactions, and sustain credible communication amid evolving threats.